DigitalAnts lead cyber defence war
12 Apr 2014
Every computer attack is a battle between the owners of a computational infrastructure and adversaries bent on using these resources for their own purposes. The owners may span multiple organisations that have limited trust between them.

Meanwhile, human adversaries are adaptively hostile, employing open-ended strategies and anti-forensic techniques. The problem of securing complex infrastructures in a dynamic hostile environment with changing adversaries cannot be solved with static defenes or uncoordinated unilateral measures.
In today's large infrastructures comprised of many collaborating organisations, the way we typically monitor cyber defence is to gather all the cyber data from across the enterprise to a single point and analyse it centrally. While this gives excellent scope of information, this approach scales poorly.
To address this challenge, the Pacific Northwest National Laboratory (PNNL) has developed a framework for decentralised coordination based on the eusocial behaviours seen in ant colonies.
The eusocial organisation in the ant colony provides a highly adaptive common defence that achieves emergent behaviour via stygmergic communication. PNNL researchers have applied these ant behaviours to cyber security in their Ant-Based Cyber Defence where humans and various software agents share the responsibilities of securing an infrastructure comprised of enclaves that belong to member organisations.
Decentralised hierarchy
The primary purpose of the Ant-Based Cyber Defence is to reduce the level of required human involvement in problem detection and resolution while retaining the human ability to intervene as desired.
The second purpose is to enable separate enclaves to cooperate in their cyber defence while maintaining their privacy and proprietary data. A hierarchy is needed to give the humans at the top a single point of access to enclave-wide security information, but the monitoring and resolution are decentralized, bringing the sensor to the data rather than vice-versa.
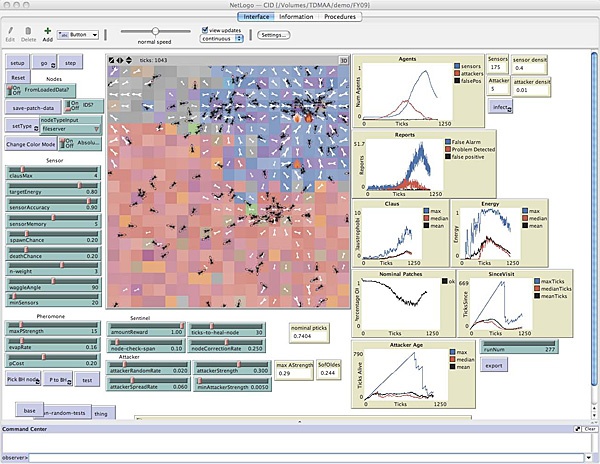
The Ant-Based Cyber Defence is made of a set of collaborating enclave hierarchies of humans and software agents. An enclave is a collection of machines owned by a single organisation and managed under a single policy. A Human Supervisor may lead multiple enclaves, each of which is led by an agent called a Sergeant. Sentinel agents autonomically monitor enclave machines, and mobile Sensor agents wander through the enclave.
Supervisors
Human supervisors provide guidance to and receive feed-back from one or more enclaves. They may take initiative as desired to inspect any element of the system, but direct human control that would destroy natural adaptation id discouraged. Supervisors need take action only when the lower-level agents encounter a problem that requires human involvement.
Sergeants
Enclave-level agents called Sergeants are each responsible for the security state of an entire enclave. Sergeants dialogue with humans to gain guidance for running the system according to human-specified business drivers and security policies. Sergeants create and enforce executable policies for the entire enclave.
Sentinels and Sensors
A host-level Sentinel agent protects and configures each monitored machine. Sentinels interact with human supervisors only when they need clarification about how to classify ambiguous evidence from the swarm of Sensor agents. The Sensors roam from machine to machine within their enclave each searching for indicators of problems uniquely derived from the set of known problem indicators.
They report discovered problems to the appropriate Sentinel. Sensors communicate by leaving digital pheromone messages that result it positive feedback, attracting a wide variety of Sensors to suspected problems.
Deployment status
The Ant-Based Cyber Defence is a technology readiness level one project that has been implemented at the Sentinel and Sensor level on a cluster of 64 Linux virtual machines. This implementation rapidly identifies previously unknown malware based on real Linux worm code. Currently, development is underway in to use the digital ant approach as a security mechanism underlying the NSF GENI testbed laboratory.